So early this week the PASS Organization (www.sqlpass.org) released their new shiny SQL Saturday website (www.sqlsaturday.com). There were a few glitches in the session submission but nothing there that isn’t expected when a major over hall of a much used application.
The Problem
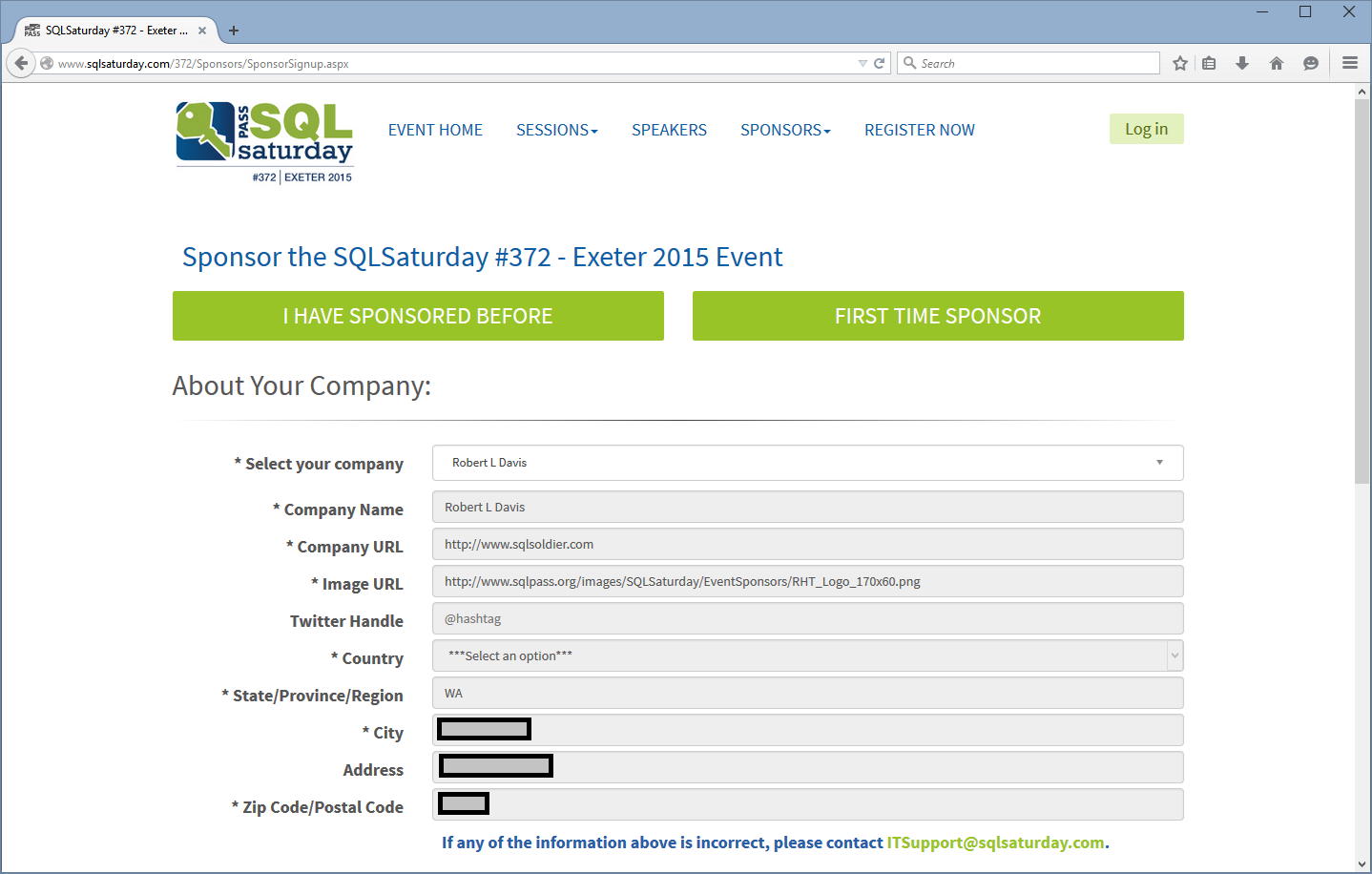
There was however a bigger problem with the system. If anyone went into the sponsor page they were able to, without even needing to log in, pull up the address which was entered for the sponsors. Now you might think that this isn’t all that big a deal because who cares if sponsors have the address of their offices shown online. Where the problem comes from is that many SQL Saturday events offer a blogger level of sponsorship for just a few dollars. This level of sponsorship usually is done by individual people who are trying to drive a little more traffic to their blog while helping a SQL Saturday out. So when filling out the sponsor address information in the past they would have put in their home address. Here for example is Robert Davis’s information when selected from the Sponsor list (with his actual address marked out).
This is obviously a problem. There are about 1390 sponsors in the system, many of which are just people with blogs who have sponsored a SQL Saturday or two for a few bucks each. Now I know it isn’t the entire PASS community, but 1000+ people’s personal home information is a pretty big leak.
The Response
PASS as an organization has responded to this problem pretty well. The problem was first reported by me on the MVP mailing list where we were discussing various things that we weren’t really thrilled with on the new SQL Saturday website (most if not all of the current board members are Microsoft MVPs so there’s actually a good reason to discuss things like this in the MVP mailing list). The board members then began bringing people form PASS HQ into the conversation with email threads outside of the MVP list. PASS immediately realized that there was a pretty big problem that needed to be addressed. How to address it became a more complex problem.
The quickest solution that PASS was able to come up with was to simply remove the page where a Sponsor can sponsor a SQL Saturday and to remove the API which that page used to pull that information the SQL Saturday database. It was a couple of hours from reporting the problem to getting the offending part of the website pulled down, but in the grand scheme of things that’s a pretty decent response time given that the developer had to do whatever magic is required to remove pages from an ASP.NET site running on Dot Net Nuke (DNN) do a quick test to make sure nothing else is broken, then publish the changes to the live website.
Later Monday night PASS decided to take the entire SQL Saturday website offline completely leaving just a maintenance message on the site while the entire site is reviewed from a security (and possibly usability) perspective with the hopes of getting the site up and running within a day or two. Now who this really sucks for is the SQL Saturday’s who are running their events this coming weekend (April 11th, 2015) which includes the SQL Saturday here in Orange County, CA. I’m presenting a session on something, at some time. I honestly have no idea what or when, hopefully the site comes back up before the weekend so that I can grab the correct slide decks and demos.
Reporting
If you are on Twitter and follow things PASS related on Twitter you probably noticed that you didn’t see anything really about this on Twitter. This was on purpose. Given that it was a data leak no one really wanted the private information of these 1000+ PASS members to be leaked online to be spread even further. The problem was reported to PASS privately (or to a small group of people known as the Microsoft MVPs) and to PASS. PASS board members were very transparent with the MVPs as to their handling of the problem and how it was going to get fixed. They did their best to keep me as the person who found and reported the problem up to date as to what was going on with the fix.
I’m sure that PASS is still trying to figure out what needs to be done as far as notification, monitoring, etc. But that involves lawyers, money and time. I’m sure that once they get that all figured out they’ll have some sort of communication to those who’s data may have been effected.
In the grand scheme of things PASS responded quickly and properly to the data leak. Hopefully we won’t have another data leak from our organization of data management professionals.
Denny