What happens to most obsolete web based applications at most companies? They sit idle on a web server for months, sometimes years. Why is this a problem? Because many of these old applications can be easily exploited via SQL Injection allowing access into the SQL Server databases which they connected to. The reason that these old apps are a great way into the SQL Server is because they are old, and were probably written before things like SQL Injection protection became more common place.
This tweet from Daniel (@DaniSQL) is a perfect example of this.
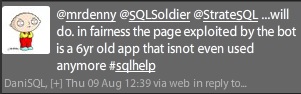
An old application that isn’t being used anymore is still available on the Internet facing web farm. Because this application isn’t being used any more it wasn’t on any lists of deployed applications, so when security audits were done it wasn’t seen as it wasn’t listed as an active application. However it was apparently able to provide a hacker with a way into the database because it was still connected to a SQL Server instance and it was susceptible to SQL Injection.
The solution to this problem is sadly easy, remove the web based application from the web farm as the application isn’t being used anywhere. It’s a lot easier than fixing the application, and a whole lot cheaper (10 minutes of a system administrator’s time versus weeks or months of a developers time).
I urge you to audit the applications and websites which are deployed to your web farms, especially the Internet facing web farms and see what’s on there. When you audit them, don’t audit them against the list of what’s there. Actually dig into the IIS config of each and every server (yes I’m well aware that doing this sucks) and actually see what’s configured on each machine. If you don’t know if an application is actually being used ask around. If it isn’t, remove it (or at least stop the site in IIS) so that you don’t have to worry about scripts breaking into your database and updating your data.
Now thankfully this current attack which is going around is just updating data, but it could easily enough be changed by the attacker to gather data as well, so do yourself a favor and protect yourself.
Denny
